MICRO DEGREE
Certified Cybersecurity Engineer
Become Cybersecurity professional in just 6 weeks
100% LIVE Interactive Classes
Become Cybersecurity professional in just 6 weeks

100% LIVE Interactive Classes
Reserve your spot today!
Basic Info
Select Offers
Application closes on:15 May 2026
Get instant access of pre-course material!
Talk to Us
We’re here to help! Reach us at:
What is in it for you?
 100% Live Classes
100% Live Classes
 Instructor-led Live Sessions
Instructor-led Live Sessions
Attend 4 weeks of instructor led live classes from the top 1% industry experts
Projects & Case Studies
Projects & Case Studies
Gain hands-on experience with projects and real-world case studies for impactful learning.
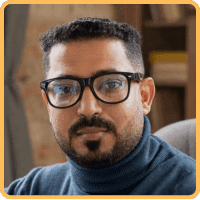
Verified Certificate
Verified Certificate
Earn a industry recognized certificate and kick start your career
Session Recordings
Session Recordings
Revisit older chapters anytime with recorded sessions
Flexible Schedule
Flexible Schedule
Choose live classes from different cohorts that fit your availability.
Hands-on Classes
Hands-on Classes
Hands-on classes to enhance your learning experience
100% Moneyback Guarantee
Grab your slot before the offer expires
Reserve your spot today!
Basic Info
Select Offers
Application closes on:15 May 2026
Get instant access of pre-course material!
Talk to Us
We’re here to help! Reach us at:
Learn from Top 1%
Sr. Managers, VPs, CXOs, Directors & Founders from companies shaping the future.

Combo Offers
Create Your Own Combo
100% Moneyback Guarantee
Available in 4 monthly installments at $56/month
Reserve your spot today!
Curriculum
Duration: 6 weeks
Max Batch Size: 15 persons
Live Sessions Schedule ![]() Sat - Sun (Weekends Only)
Sat - Sun (Weekends Only) ![]() Timing 7:00 AM - 9:00 AM / 8:30 AM - 10:30 AM / 11:00 AM - 1:00 PM / 5:00 PM - 7:00 PM / 7:30 PM - 9:30 PM EST
Timing 7:00 AM - 9:00 AM / 8:30 AM - 10:30 AM / 11:00 AM - 1:00 PM / 5:00 PM - 7:00 PM / 7:30 PM - 9:30 PM EST
- Introduction to Ethical Hacking
- Information Security Overview
- Information Security Threats and Attack Vectors
- Ethical Hacking Concepts
- Information Security Controls
- Penetration Testing Concepts
- Information Security Laws and Standards
- Footprinting and Reconnaissance
- Footprinting through Search Engines, Web Services, and Social Networking Sites
- Website Footprinting
- Email Footprinting
- Competitive Intelligence
- Whois, DNS, and Network Footprinting
- Footprinting through Social Engineering
- Footprinting Tools
- Countermeasures
- Footprinting Pen Testing
Mentors
13+ Years, CyberSecurity Sr. Manager, PayTm
15+ Years, Cybersecurity Manager, Deloitte
Course Includes

LIVE Interactive Sessions

Quizzes, Assignments & Projects

Study Materials & Session Recordings

Certificate
Tools Covered

Course Includes

LIVE Interactive Sessions

Quizzes, Assignments & Projects

Study Materials & Session Recordings

Certificate
Course Pre-requisites
.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Basic understanding of computer networking concepts (TCP/IP, OSI model, common protocols)
Basic understanding of computer networking concepts (TCP/IP, OSI model, common protocols).ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Familiarity with Linux and Windows operating systems
Familiarity with Linux and Windows operating systems.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Foundational knowledge of IT infrastructure and system administration
Foundational knowledge of IT infrastructure and system administration
Outcomes
.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Conduct comprehensive footprinting and reconnaissance to map an organization's attack surface using search engines, WHOIS, DNS, and social engineering techniques
Conduct comprehensive footprinting and reconnaissance to map an organization's attack surface using search engines, WHOIS, DNS, and social engineering techniques.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Perform network scanning and enumeration to discover live hosts, open ports, running services, and exploitable information using industry-standard tools
Perform network scanning and enumeration to discover live hosts, open ports, running services, and exploitable information using industry-standard tools.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Analyse system vulnerabilities using scoring systems and assessment tools to produce actionable vulnerability reports
Analyse system vulnerabilities using scoring systems and assessment tools to produce actionable vulnerability reports.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Implement system hacking techniques including password cracking, privilege escalation, and covering tracks to simulate real-world attacks
Implement system hacking techniques including password cracking, privilege escalation, and covering tracks to simulate real-world attacks.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Identify and analyse malware threats including trojans, viruses, and worms, and deploy effective countermeasures and anti-malware solutions
Identify and analyse malware threats including trojans, viruses, and worms, and deploy effective countermeasures and anti-malware solutions.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Execute network sniffing attacks such as ARP poisoning, DNS poisoning, and MAC attacks, and apply detection and prevention techniques
Execute network sniffing attacks such as ARP poisoning, DNS poisoning, and MAC attacks, and apply detection and prevention techniques.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Assess the security of web servers, web applications, wireless networks, mobile platforms, IoT devices, and cloud environments
Assess the security of web servers, web applications, wireless networks, mobile platforms, IoT devices, and cloud environments.ffb97545.png&w=16&q=75&dpl=dpl_88JeRGaguJJYkAGtmBYvYqQv1iH2) Design and implement defensive strategies including IDS/firewall evasion countermeasures, session hijacking prevention, and cryptographic protections
Design and implement defensive strategies including IDS/firewall evasion countermeasures, session hijacking prevention, and cryptographic protections
Projects You Will Build
Practical, enterprise-grade projects that reflect real industry challenges
Enterprise Network Penetration Test
Perform a full-scope penetration test on a simulated corporate network, starting from footprinting and reconnaissance through network scanning, enumeration, vulnerability analysis, and exploitation. Document all findings using industry-standard reporting formats, including risk ratings and prioritized remediation recommendations.
Malware Analysis and Incident Response Lab
Analyse a set of real-world malware samples including trojans, viruses, and worms in a sandboxed environment to determine their behavior, propagation methods, and impact. Develop and implement countermeasures, anti-malware configurations, and an incident response playbook to contain and eradicate the threats.
Web Application and IoT Security Assessment
Conduct a comprehensive security assessment of a vulnerable web application and an IoT device network, identifying weaknesses such as SQL injection, cross-site scripting, insecure authentication, and unencrypted communications. Implement remediation measures including secure configurations, network segmentation, and cryptographic controls, then validate fixes through retesting.
for successfully completing the 'Certified Cybersecurity Engineer' course conducted from 02 Apr 2026 to 14 May 2026
Add a Industry Recognized
Certificate To Your Resume
Industry Recognized
Certificate
Learn the best from the best

Career Advancements
Elevate your career with a respected certificate

Industry Respect
Gain credibility in the field

Networking
Connect with experts and peers

Opportunities
Attract exciting job prospects and promotions

for successfully completing the 'Certified Cybersecurity Engineer' course conducted from 02 Apr 2026 to 14 May 2026
100% Moneyback Guarantee
Top 1% Recruiters - Get interview access to 550+ Companies

Frequently Asked Questions
Everything you need to know about the course
You should have a basic understanding of computer networking concepts (TCP/IP, OSI model), familiarity with Linux and Windows operating systems, and foundational IT infrastructure knowledge. No prior cybersecurity or ethical hacking experience is required.
The curriculum covers ethical hacking fundamentals, footprinting and reconnaissance, network scanning and enumeration, vulnerability analysis, system hacking, malware threats and analysis, network sniffing attacks and countermeasures, web server and web application security, wireless and mobile security, IoT and cloud security, social engineering, session hijacking, DoS attacks, IDS/firewall evasion, and cryptography.
Over the 6-week duration, you should plan to dedicate approximately 15-20 hours per week, including video lessons, hands-on labs, and project work. The course is intensive due to the breadth of cybersecurity topics and practical exercises involved.
You will complete practical labs in real-world cybersecurity scenarios, including footprinting exercises, network scanning and enumeration, vulnerability assessments, system hacking simulations, malware analysis, sniffing attack execution, web application penetration testing, and three capstone projects that simulate professional engagements.
This certification prepares you for roles such as Cybersecurity Analyst, Penetration Tester, Security Consultant, Incident Response Specialist, and Information Security Engineer. The hands-on training and industry-recognized methodology provide practical skills that employers actively seek, making you job-ready upon completion.
You will gain hands-on experience with Kali Linux, Nmap, Metasploit Framework, Wireshark, Burp Suite, Nessus, and various enumeration and footprinting tools. These are industry-standard tools widely used by cybersecurity professionals and penetration testers.
The Micro Degree course is an online LIVE course, where LIVE sessions will be conducted online on our Classroom platform. Prior to the start of the course, you'll receive preparatory material in the form of recorded content which can be access on the same platform.
In this course instructors will use English language for teaching.
Upon successful registration, you will receive a confirmation email on your registered email ID. In this email you will receive login details for your newly created account on the Edyoda Classroom platform (https://classroom.edyoda.com). Additionally, you will receive a PDF guide containing step-by-step instructions on how to utilize the platform to access live sessions and learning materials.
Our instructors are the industry experts with a minimum working experience of 10 years with a strong technical and teaching background. They bring industry knowledge and practical expertise to the course.
Yes, the course includes online assignments, quizzes, and a final project to reinforce your learning and assess your proficiency in Certified Cybersecurity Engineer.
Yes, you can interact with instructors and fellow students through discussion forums, live Q&A sessions. We encourage a supportive learning community.
We offer a 100% money-back guarantee to ensure your complete satisfaction. If you're not satisfied, you can request a full refund within 3 days of purchase or before the second session, whichever comes earlier. Simply contact our support team(support@edyoda.com) with your purchase details, such as the order ID or email address, and share your reason for the refund. Requests made after 3 days or after the second session will not be eligible for a refund. There are no hidden charges, you will receive the full amount paid. Refunds are processed within 7–10 business days and credited back to your original payment method.
Recommendations